Key Strategic Developments and Emerging Changes Shaping – openPR.com
Key Strategic Developments and Emerging Changes Shaping openPR.com Go to Source Author:
Key Strategic Developments and Emerging Changes Shaping openPR.com Go to Source Author:
Analytics and Data Science News for the Week of May 8; Updates from Acceldata, Databricks, Dataiku & More Solutions Review Go to Source Author:
Writing code has always been the most time- and resource-intensive task in software development. AI is changing that, and faster than most engineering organizations are prepared for. Tools like Claude Code and Cursor are already handling significant parts of code construction, freeing developers to spend more time on requirements, architecture, and design. But that shift…

A critical pre-authentication remote code execution vulnerability in Marimo, an open-source Python notebook platform owned by AI cloud company CoreWeave, was exploited in the wild less than 10 hours after its public disclosure, according to the Sysdig Threat Research Team. The vulnerability, tracked as CVE-2026-39987 with a severity score of 9.3 out of 10, affects all Marimo…

Announced at JavaOne, Project Detroit proposes to break down the walls between Java, Python, and JavaScript. Also in this report: Better ways to instrument your code with Python’s new built-in sampling profiler, another run at using AI locally to rework a Python project, and the question on everyone’s mind right now (surely): What does OpenAI…

Thirteen critical vulnerabilities have been found in the vm2 JavaScript sandbox package that could allow an attacker’s code to escape the container and do nasty things to IT environments. As a result, developers using this library in their applications are urged to update the software to the latest version, which is currently 3.11.2. The warnings…
Verint Genie Bot Honored Across Award Programs for Delivering AI-Powered Outcomes Business Wire Go to Source Author:
LegalOn Expands Its AI Productivity Platform With Vault, Turning Contracts Into Business Intelligence Business Wire Go to Source Author:
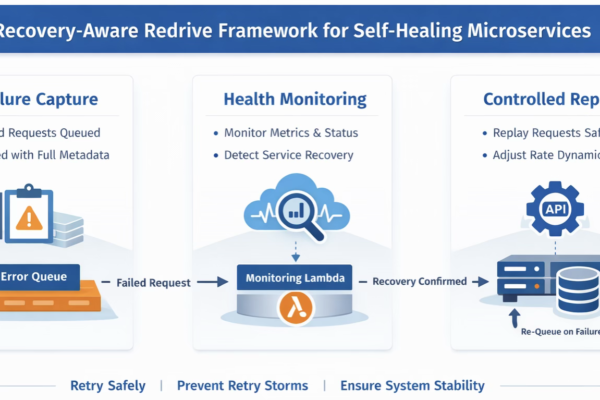
Cloud-native microservices are built for resilience, but true fault tolerance requires more than automatic retries. In complex distributed systems, a single failure can cascade across multiple services, databases, caches or third-party APIs, causing widespread disruptions. Traditional retry mechanisms, if applied blindly, can exacerbate failures and create what is known as a retry storm, an exponential…