Enterprise environments are changing quickly as organizations adopt cloud platforms, automated infrastructure, and continuous delivery pipelines. Software updates are released more often, and systems are set up automatically using infrastructure-as-code automation tools. While this acceleration allows organizations to deliver software and services faster, it also creates new challenges for security teams responsible for protecting constantly changing systems.
Today’s enterprise security teams must defend environments that are dynamic, distributed, and difficult to fully observe. As organizations adopt new platforms and development practices, the attack surface grows. Security teams must detect and respond to threats across these environments while maintaining clear visibility into what is happening in real time.
Traditional security testing models were not designed for this pace of change. Organizations have long relied on penetration tests and red team engagements to simulate real attacks and uncover weaknesses. These assessments remain valuable, but they typically occur at fixed intervals and may not reflect the current state of the environment. By the time results are delivered and remediation begins, the environment may already look very different.
As enterprise environments evolve more quickly, security testing must also become continuous. Continuous purple teaming offers one practical way to achieve this by bringing offensive and defensive security teams together in ongoing workflows, driven by real-world threats and grounded in measurable outcomes.
Threat intelligence as the driver of continuous validation
One of the most important elements of continuous purple teaming is what drives the simulations. Running attack techniques on a schedule is not enough. Without a continuous feed of curated, prioritized threat intelligence, organizations risk simulating generic activity that does not reflect what is actually targeting them. In that case, the exercise becomes closer to breach and attack simulation tooling rather than true purple teaming.
Continuous purple teaming relies on up-to-date threat intelligence aligned to the organization’s industry, geography, and technology stack. This intelligence determines what to test, why it matters, and how often it should be exercised.
In practice, this means mapping intelligence to a common framework such as MITRE ATT&CK. This provides a shared taxonomy for adversary behavior, helping teams align simulations, detection coverage, and reporting while identifying gaps. Without this grounding, teams are training against yesterday’s threats. With it, they validate readiness against what is targeting them today.
Moving security validation into daily operations
Historically, many organizations approached security validation as a series of isolated assessments. Red teams conducted engagements designed to emulate real attackers, producing reports that described vulnerabilities and potential attack paths. Blue teams then reviewed these findings and began remediation work. This model has value because it reveals complex weaknesses that automated scanners often miss. However, it also introduces gaps between testing cycles. When infrastructure and applications change frequently, those gaps can leave organizations uncertain about the current effectiveness of their security controls.
Continuous purple teaming also generates data that helps organizations measure how well their detection and response capabilities perform during simulated attacks. Offensive simulations occur regularly and sometimes automatically, allowing defenders to observe how detection systems and response workflows perform in realistic attack scenarios.
Security engineers can then adjust logging strategies, detection rules, and response playbooks immediately. This model aligns security validation with the operational flow of modern enterprises. Instead of testing defenses occasionally, organizations continuously evaluate how their security tools and processes perform under realistic conditions.
Just as importantly, these exercises are not performed in isolation. The value comes from the collaboration between teams. Red team operators explain how and why a technique works. Blue team analysts share what they see, or do not see, in telemetry. Together, they refine detections, improve visibility, and strengthen response workflows.
This real-time knowledge transfer is what makes purple teaming effective. The focus is on building shared understanding between offense and defense.
Atomic testing and attack chain simulation
Not all simulations serve the same purpose, and mature programs distinguish between two types of testing: atomic testing and chain-based testing. Both approaches are necessary.
Atomic testing focuses on individual techniques. For example, testing whether endpoint detection tools identify credential dumping from LSASS or whether a specific persistence mechanism triggers an alert. Atomic tests provide breadth and speed. They help teams quickly identify gaps in visibility or detection logic.
Chain-based testing simulates full attack paths. This might include an initial phishing attempt, followed by credential access, privilege escalation, lateral movement, and ultimately data exfiltration. Chain-based simulations provide depth. They expose whether detections correlate across stages, whether alerts are understood in context, and whether response processes actually work end-to-end. They also reveal breakdowns in handoffs between teams and gaps in orchestration and automation.
Building environments for realistic attack simulation
To operationalize purple teaming effectively, organizations need environments where realistic attack scenarios can be executed safely. Many enterprises build these environments as cyber ranges or laboratory infrastructures that mirror production architectures as closely as possible. These environments may replicate identity systems, cloud services, endpoint devices, and network segmentation controls. The goal is to create a controlled environment where both offensive and defensive teams can collaborate. Red team operators can simulate adversary behavior while blue team analysts monitor telemetry, investigate alerts, and practice incident response procedures.
These environments support both validation and training. Security engineers can test new detection strategies and logging configurations, while analysts gain experience investigating incidents that resemble real attacks. Because exercises take place outside of production systems, teams can experiment with new techniques without disrupting business operations.
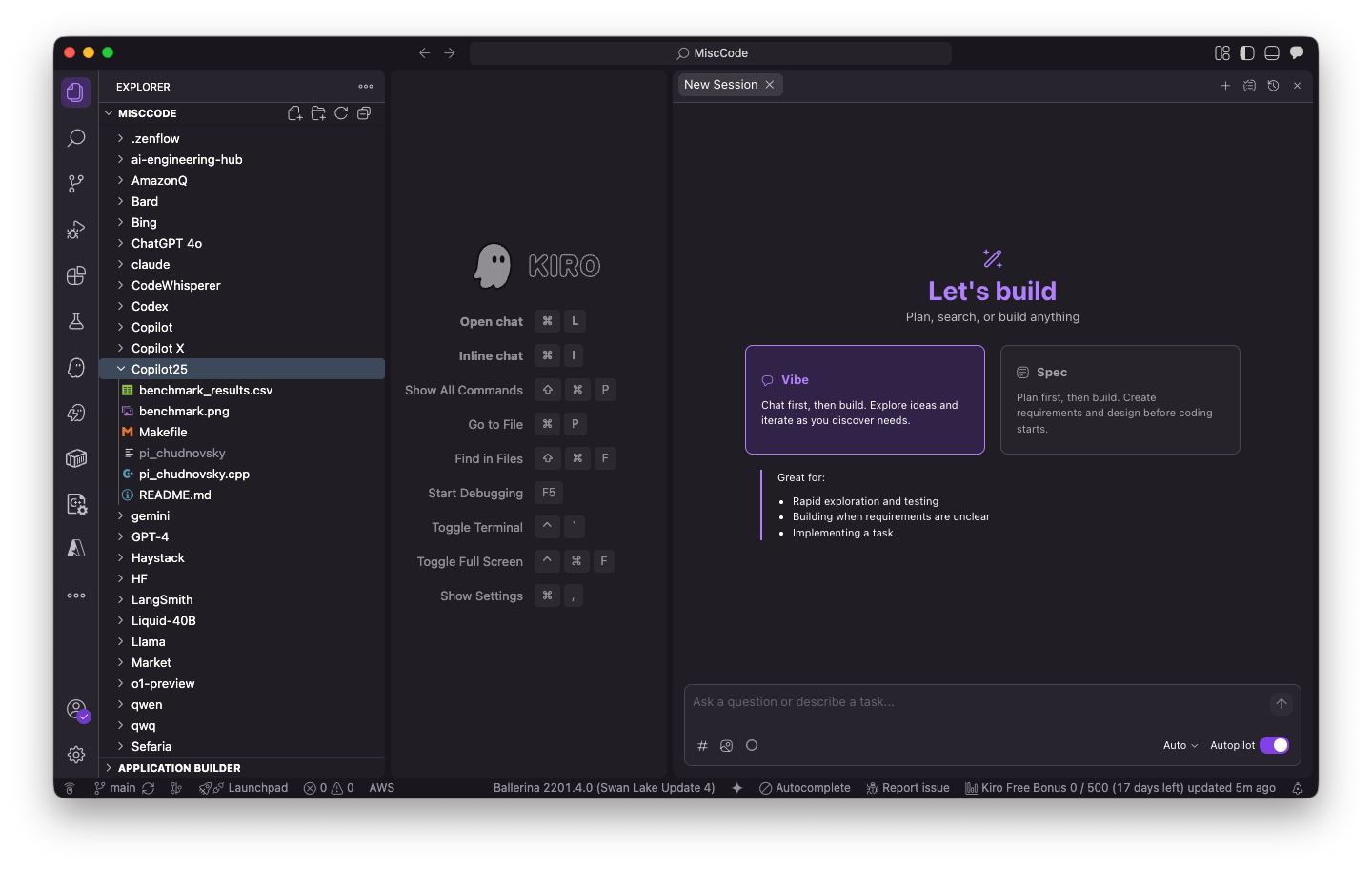
Hands-on environments have become an important component of modern cybersecurity training and operational readiness. Platforms that provide simulated labs and realistic attack scenarios help practitioners develop practical skills across both offensive and defensive domains while working through complex security challenges.
Operationalizing purple teaming at scale
Automation plays a key role in making continuous purple teaming practical at enterprise scale. Infrastructure-as-code tools allow teams to create testing environments that closely mirror their production systems. Cloud resources, identity services, endpoints, and network configurations can all be set up automatically.
Once the environment is in place, attack simulations can also run through automation. Security teams can script common adversary techniques aligned to MITRE ATT&CK such as credential harvesting, privilege escalation, lateral movement, and data exfiltration. These simulations can run on a schedule or be triggered automatically when infrastructure changes occur.
Because the same scenarios can be run repeatedly, teams can see how their defenses perform over time. If a new deployment introduces a visibility gap or changes how detection tools behave, the next simulation can quickly reveal the issue.
Continuous purple teaming also gives organizations data about how well their detection and response processes work during simulated attacks. Security teams can track metrics such as:
- Detection coverage: Which ATT&CK techniques are exercised and observed
- Time to detection: How long it takes monitoring systems to identify suspicious activity
- Time to investigation: How long analysts need to triage alerts and begin analysis
- Response effectiveness: How well automated or manual response actions work during simulations
However, detection coverage alone is not enough. An alert does not automatically mean effective detection. Mature programs evaluate detection quality. This includes whether the correct alert fired, at the right fidelity, with the right context, and whether it was actionable for the analyst. Detection quality matters as much as detection coverage.
Preparing for AI-enabled threats
AI is influencing both offensive and defensive cybersecurity practices. Threat actors increasingly use AI tools to automate reconnaissance, generate phishing content, and accelerate malware development. These capabilities allow attackers to scale operations and experiment with new techniques more rapidly.
Purple teaming environments provide a controlled setting where organizations can safely explore these emerging threats. Red teams can simulate AI-assisted attack scenarios such as automated reconnaissance workflows or large-scale phishing campaigns generated by language models. These exercises help defenders observe how AI-driven attack techniques interact with existing monitoring systems.
These environments also support AI red teaming, where organizations intentionally test how generative AI systems and AI-enabled tools might be abused by adversaries. Security teams can simulate prompt manipulation, automated social engineering, and AI-generated attack workflows in order to evaluate defensive controls and detection strategies.
Defensive teams can also explore how AI supports their own operations. AI-assisted investigation tools, anomaly detection systems, and automated threat analysis platforms can be tested in controlled environments before being deployed in production security systems.
Security validation at the speed of enterprise infrastructure
Enterprise infrastructure will continue to evolve as organizations adopt new cloud services, automation frameworks, and development practices. Security programs must adapt to this pace of change to remain effective.
Continuous purple teaming provides a practical framework for aligning security validation with modern enterprise operations. Automated attack simulations, reproducible testing environments, and integrated security telemetry allow organizations to validate defenses continuously rather than intermittently. This approach helps security teams identify weaknesses earlier and refine their defenses through constant feedback. Analysts gain experience responding to complex threats, while security leaders gain clearer visibility into how well their monitoring and response capabilities perform.
In an environment where infrastructure evolves rapidly and attackers continue to innovate, continuous validation becomes a key component of resilient enterprise security operations. Purple teaming gives security teams a practical way to test their defenses as infrastructure evolves.
—
New Tech Forum provides a venue for technology leaders—including vendors and other outside contributors—to explore and discuss emerging enterprise technology in unprecedented depth and breadth. The selection is subjective, based on our pick of the technologies we believe to be important and of greatest interest to InfoWorld readers. InfoWorld does not accept marketing collateral for publication and reserves the right to edit all contributed content. Send all inquiries to doug_dineley@foundryco.com.
Go to Source
Author: